A Cyber security specialist’s guide to be safe in the virtual world
“Trust, trust is the most vulnerable trait a human can have” – Imsohacked.
There is a reason why Gautam Mayekar used this line in his first book from the Hacker series and he continues to stress on the same as he writes more fictional stories based in the hacker world.
Being in cyber security domains, he has been exposed to a variety of real-world hacking scenarios and the most exploitable and damaging ones have been those with user involvement. Also an ethical hacker, Gautam shares some insightful tips for all on how to be safe in this virtual world.
It’s not just a click
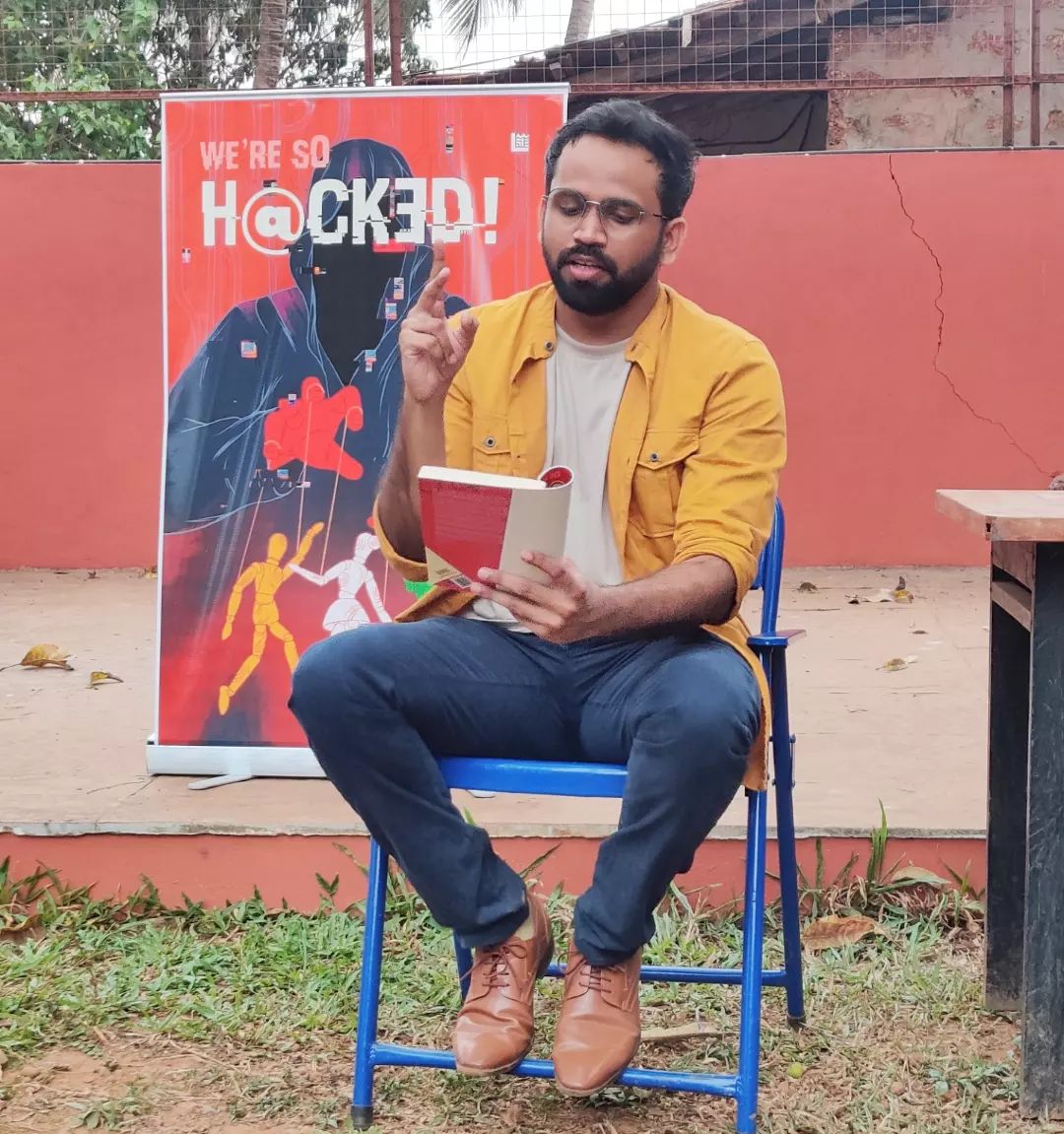
What happens when you click on any URL or any button on the internet? A chain reaction. It sets of multiple requests and responses behind the scene to actually hit the resource that is present somewhere out there on the server and present it to you. The server is most often in the control of the provider of those resources. But it’s the front end that can potentially change. Now, what if the attacker manages to present to you a crafted user interface?
And that’s exactly what the attackers do to exploit your click, your trust, and then potentially steal your secrets or/and carry out malicious actions which you would have never indented to.
Common web attacks
There are many web application vulnerabilities that are leveraged by the attackers depending on the system they are onto. But the major ones which are interesting for our current topic of discussion are: (1) Click Jacking (2) Cross-site Request Forgery (3) Phishing.
Click Jacking is the malicious practice of manipulating a website user’s activity by concealing hyperlinks beneath legitimate clickable content, thereby causing the user to perform actions of which they are unaware. Even the mighty Facebook suffered from this issue. You can read more about it here –An Example Of Likejacking (Facebook Clickjacking) | Zscaler
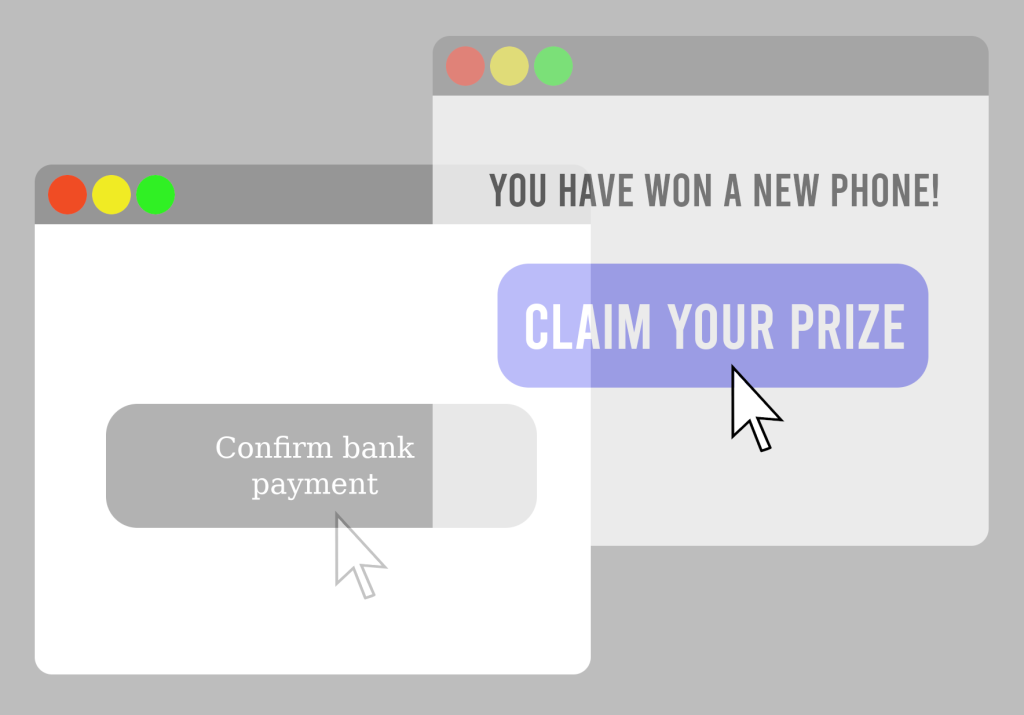
Cross-site Request Forgery is a type of malicious exploit of a website where unauthorized commands are submitted from a user that the web application trusts. An attacker tricks innocent victim into submitting a web request that they did not intend. This may cause actions to be performed on the website that can include inadvertent client or server data leakage, change of session state, or manipulation of an end user’s account. Many applications and websites have been vulnerable to CSRF attack in past, including the giant NETFLIX. (CSRF- Netflix and Youtube are victims of it | by Beribey | Medium)

Phishing got its name from “phish” meaning fish. It’s a common phenomenon to put bait for the fish to get trapped. Similarly, phishing is an unethical way to dupe the user or victim to click on harmful sites. The attacker crafts the harmful site in such a way that the victim feels it to be an authentic site, thus falling prey to it. The most common mode of phishing is spam emails that appear to be authentic. As per 2020 study, Phishing is by far the most common attack performed by the attackers.
How security professionals are preventing them
Ethical hackers try to find these attacks in their in-house lab environment and inform the respective app owners or developers with whom they are either contracted with or freelancing. There are also many bug bounty websites that have come up where in you can responsibly disclose any such issues that you find.
Some of the key areas to note here:
- Having a simple header checks can prevent such attacks – Web applications should include security headers in their requests/responses for eg. X-frame Options -DENY, Referer and so on.
- Including a token with web requests can add an extra layer of defence and help identify legitimate requests which were meant to originate from victim’s clicks.
- Design reviews can help identify the broken access control and counter these exploits via clicks. For example, for a changing-password feature, having an additional dialogue box asking for the old password or something like “Do you really want to change the password?” can add two-layered defence.
How can we, as users, stay safe?
Knowing how developers can try and strengthen websites, it ultimately boils down to how a user thinks and clicks. Some of the points that we can note during browsing are:
- Double check the URL or the website link which you are clicking, confirm whether it is a legitimate one.
- Whenever you receive an email or SMS asking you to click on some links or provide certain information, do a Google check to verify legitimacy.
- Always make sure you do your banking transactions in a different browser than the one in which you browse generally.
- Sometimes, the URLs are garbled. For examples, in a phishing scam, Indigo.com was written as !ndigo.com. Look out for these discrepancies and make sure you are logging into the correct website.
- Never reveal any secret token (OTP’s, Passwords, ID’s, etc.,) over a phone call or email, unless it is from the source where it is originated.
- Check for the email message digest and verify the authenticity of the signatures.
In addition to working as a Lead Security Engineer at John Deere, Gautam Mayekar loves weaving stories around India’s cyber secrets. With 2 books released and selling well on all leading platforms and the third book of the trilogy in creation, he makes the readers immerse into the cyber world through blending technical and complex concepts with engrossing stories.
One thing he always urges everyone to remember: Your click is important, use it wisely.
To learn more insights about technology and how to be safe in the virtual world, you can Engage / Book / Hire / Performance Fees / Enquire for Charges for the top keynote speakers via engage4more’s passionate team. Our working relations with over 2,500+ Keynote / motivational speakers, and artists come with an assurance of best-suited artist suggestions for your event with pacy bookings and great prices. Also, enjoy our value adds like complimentary quizzing for your events along with free publicity by our post-event coverage via our social media handles!
Start your keynote speaker booking journey here.